
COVID-19 has had so many negative effects on the world that it’s easy to overlook the fact that vehicle theft in North America has risen dramatically (anywhere from 20% to over 70%, depending on your location and news source). And although pandemic conditions are partially to blame (people are home more and cars are parked in the same location regularly, making it easy for thieves to plan), technology is also at fault. Although there’s little we can do to end the pandemic (wear a mask!), there’s actually a lot we can do to prevent vehicle theft. Let’s discuss.
Modern Vehicle Theft: What You Need to Know
First and foremost, forget everything you know about vehicle theft. The days of teenagers breaking into your parents’ car, hotwiring it and taking it for a joyride, are gone. As are the days of local thugs stealing your truck, chopping it up in a nearby warehouse and selling the parts. The majority of vehicle theft today features a much more sophisticated attack method and more concerningly, a very lucrative and orchestrated business back-end marketplace to monetize your stolen car/truck/motorcycle.
The Relay Attack
Simply put, the most vulnerable component of your vehicle’s security system is the wireless unlock and ignition feature that has become standard on modern cars, trucks (and now motorcycles). Thefts generally occur overnight (3:30am tends to be the sweet spot for thieves are nearly everyone is alseep) with vehicles that are parked outdoors, either in driveways or on the street. Thieves arrive by car or on foot, armed with handheld devices that are specifically designed to capture and replay keyless entry and ignition device frequencies. Much like your home wifi network, your vehicle’s key fobs emit a passive digital signature – this is what allows you to walk up to your car and have it unlock or start without the need to touch the fob. The thieves use capture devices that are inexpensive and readily available on Amazon and eBay (linking to the devices would be counter-productive so you’ll have to take my word for it) to intercept the signal from your fob and trick your vehicle into thinking it’s nearby. This allows the thieves to unlock a vehicle, start it and drive it off within seconds (as shown in the CNN video below). 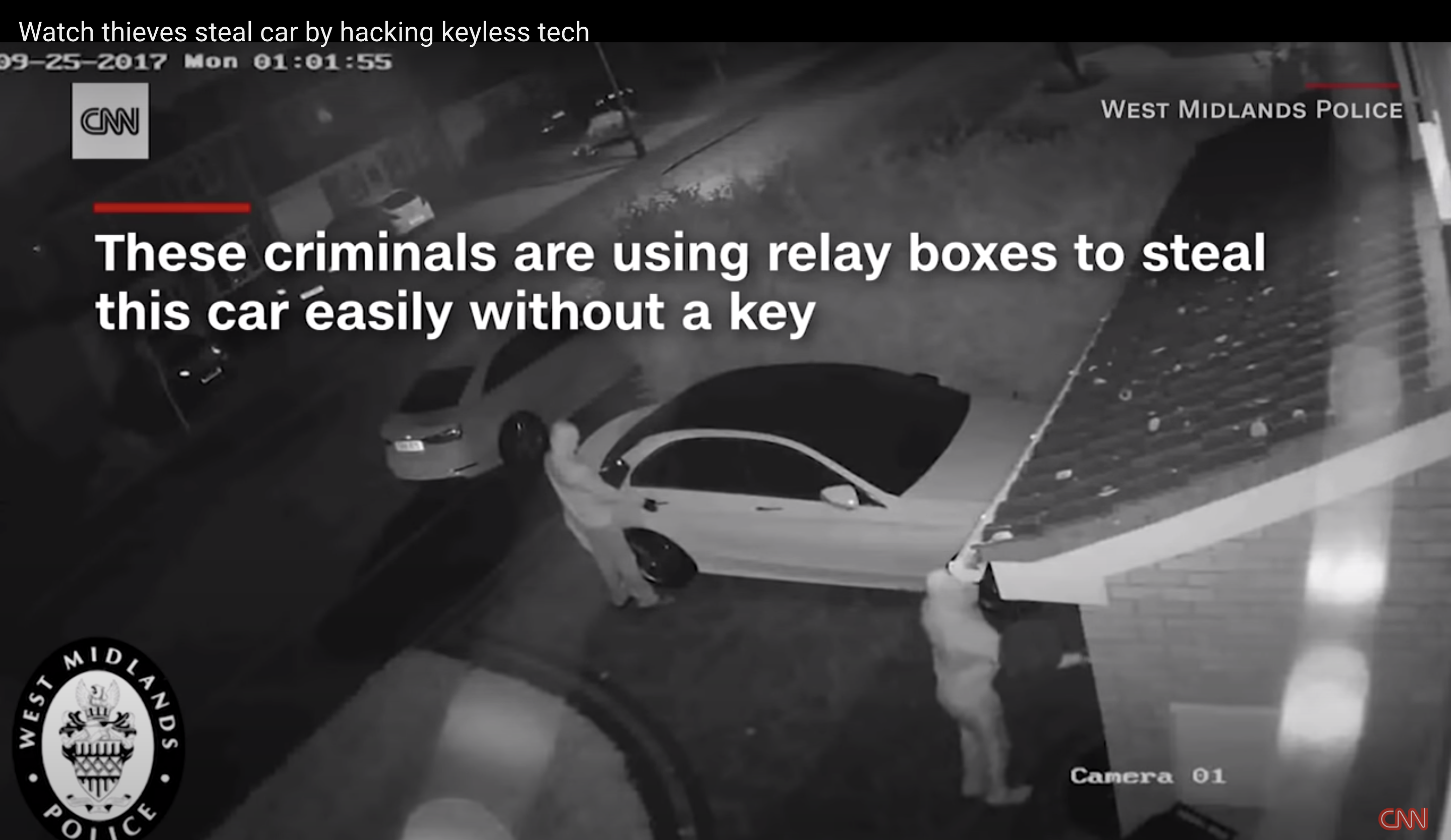
The Replay Attack
There are several permutations of this attack, tailored to the target vehicle’s vulnerabilities. One of these is the “replay attack” where a device can simply copy the code from the key fob when the button is pressed (for example, if you unlock your car in a grocery store parking lot), only to “replay” that code at a later date. Since the code on some less secure vehicles is static, once an attacker has the code copied, it will work any time to both unlock or start the vehicle.
Where do Stolen Vehicles Go?
Although what we’ve covered so far is greatly concerning, what’s of even greater concern is what happens next. The thieves who stole your vehicle are but the tip of the spear in an operation that often spans multiple continents for the processing of your stolent property. From your driveway or street, the vehicle is taken to a nearby location where it gets loaded into a truck or shipping container (rendering GPS tracking useless -more on that later). It then makes its way to a port where it is shipped overseas. With ample time to reprogram or retrofit the electronics, the bad guys are able to get your vehicle back into running condition and ready for its new owner before it reaches land.
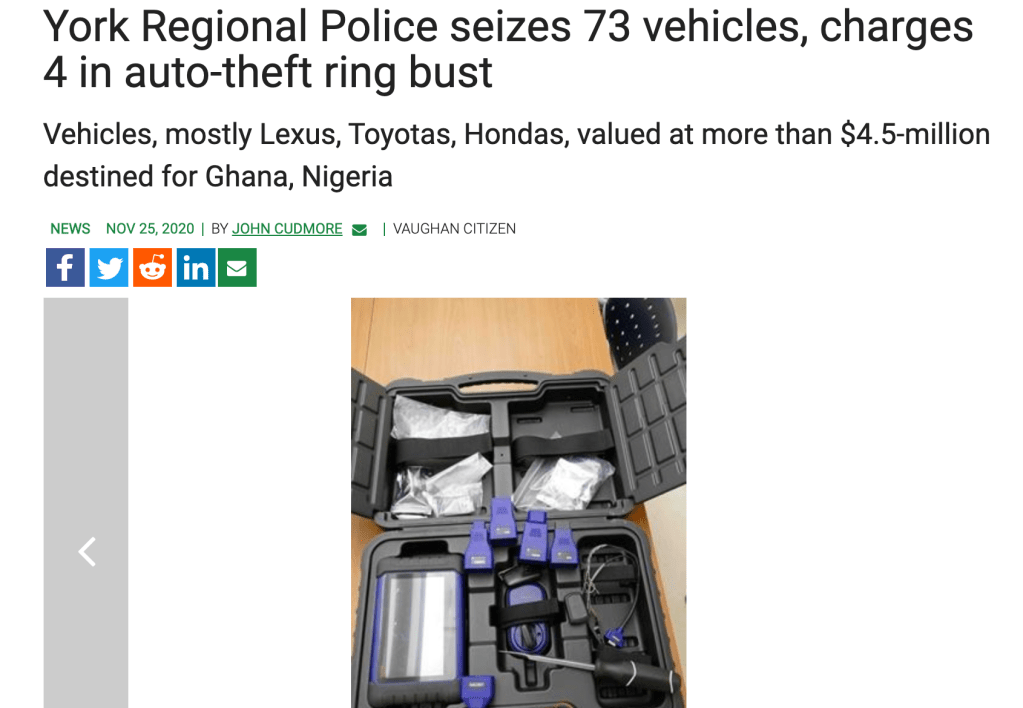
In many cases, your vehicle was sold on the dark web through a virtual marketplace, before the thieves even stole it! Africa and certain Eastern European countries have historically been destinations for stolen vehicles and in certain cases, police believe that foreign governments may even be involved. Similar to the “drug dealer model”, a given crime syndicate can have many “feeder” subsidiaries, all stealing vehicles from different neighborhoods and delivering them to a central point for processing. In contrast to petty theft which occurs more frequently in low income areas (“ghettos”), this newer form of crime is widespread around densely populated urban centres. Living in a “nice family neighborhood” perhaps increases your vulnerability due to the number of new, desirable vehicles and the predictability of behavior patterns. To re-iterate, we are dealing with organized crime as a business, on a global level – a far cry from the tennager joyrides of yesterday.
Is Your Vehicle At Risk?
If you drive a vehicle that’s less than 5 years old and has keyless entry and ignition, the short answer is yes as most vehicles are succeptible to the above-described techniques. A study from ADAC Automotive which recently tested several makes and models for this particular vulnerability can be found here. Although there’s less data available about motorcycles, the same exploits are possible and are on the rise, as more and more bikes (usually higher end models) go keyless.
Preventative Measures
Fortunately, there are ways to protect against these attacks. The adage in cybersecurity is that there will always be a tradeoff between security and convenience -something to consider as you weigh your options.
Park Indoors
Although not possible for everyone, underground parking in condo buildings virtually eliminates relay attacks (but not replay attacks or common “pick-it-up-and-put-it-in-the-back-of-a-van” motorcycle thefts) as your keys are likely several floors above the parking garage. Those living in residential neighborhoods who have access to a locked garage are also much less likely to be targeted. Remember that this digital theft prioritizes volume (of vehicles stolen) and thieves prefer to come and go quietly without the use force.
Farraday Bags

Since a large percentage of the attacks require access to the signal from your fob, preventing the signal from leaving your house is an easy and secure way to protect against the relay attack. Storing your keys in a metal container will block most of the signal or you can purchase a farraday bag from brands like Mission Darkness on Amazon.
Security Cameras

Make no mistake, thieves will still steal your vehicle if you have video surveillance around your property but it doesn’t hurt to have proof of what happened and it may deter some thieves. Whether that’s for your own personal comfort, for insurance purposes or because you want to intervene if someone is detected on your property (not recommended). Cameras from brands such as Nest have computer vision that can detect movement and people and even alert you if someone is within a designated perimeter.
Physical Anti-Theft Devices (The Club, Disklok…)

The tried and true steering wheel lock (eg. The Club) still has a place in automotive security -albeit a nuanced one. Yes, it will deter thieves, but the types of thieves it will deter are most likely the “teenager joyride” type, and not the organized crime syndicate variety. Take it from someone who has video (and audio) of thieves cutting through his steering wheel to remove one such device after having performed a replay attack. Indeed -although the device itself may be indestructible, your steering wheel is made out of rubber and can be sawed through in a matter of minutes. There are similar, higher security devices (such as Disklok) which cover the entire steering wheel for increased security, albeit at a detriment to convenience.
Alarm Systems (Viper, Clifford, Compustar…)

Aftermarket alarms can provide a 2nd layer of security, beyond the often vulnerable OEM systems. They can also add an audible alarm to help deter theft and some modern 2-way systems can also send a notification to your phone. When contemplating any such system, pay particular attention to the encryption used between the fob and receiver as many aftermarket systems are subject to the same vulnerabilities as the OEM fobs. It’s also a good idea to ask yourself the question: “what are you truly prepared to do if you find someone attempting to steal your vehicle?” and it it really worth a potential physical confrontation?
Kill Switches & Immobilizers (Igla, Ravelco…)

The most old fashioned but perhaps most secure theft deterrents available. Kill switches will prevent the vehicle from being started unless a switch is toggled or a button is pressed. These are often installed in hidden locations and would require a would-be thief to know its wherebouts in order to start the vehicle. Similarly, immobilizers like Ravelco require a fob to be physically plugged into a dedicated receiver that’s often hidden inside the vehicle. Without this physical fob, the vehicle cannot be started. The downside to either of these systems is that they often disable OEM remote start features so think of them as a tradeoff.
Stolen Vehicle Recovery Systems (LoJack, GPS trackers, )
![]()
The first question to ask yourself when considering (or relying on) a recovery system is whether or not your actually want your stolen vehicle back in the event of a theft. Since all the solutions in this category are aimed at finding your vehicle once it’s been stolen, the value proposition is actually quite different. In many cases, recovered vehicles have been damaged or are missing parts so “recovery” may entail a lot of repairs in addition to the hassle associated with insurance claims.
In summary, prevention is by far and away your best bet when it comes to protecting cars, trucks and motorcycle. One thing is for certain, this type of theft will continue to rise as vehicles become increasingly digital so it’s best to be educated and prepared.

Leave a comment